What are the seven layers of the OSI model? Let’s demystify the application, presentation, session, transport, network, data link, and physical layers to better understand how we digitally communicate with one another.
I spent a great portion of my career in telecommunications. While I was there, I worked on an assortment of jobs that helped me to connect thousands of people to the internet from the physical side: installing modems, running fiber optics to commercial and residential areas, and even placing utility poles into the ground and attaching connections on them to light up the city with the internet. My career also allowed me to work on cloud farms setting up servers, databases, and network racks.
Before I got into web development as a career at Sparkbox, I always wondered how all of the hardware components I worked with properly transferred all that data through so many conduits. I wrote this article to demystify some of the architecture that allows us to communicate with one another using devices, like our phones, computers, smart home devices...or anything that uses the internet.
Transferring data over Wi-Fi or cabling is no easy task…but it’s not magic either. The ability to communicate with one another in a matter of seconds is a luxury that we may sometimes take for granted. During my journey to understand network communication better, I stumbled across different resources about how computer systems communicate, mainly the TCP/IP Model and the Open Systems Interconnection (OSI) Model. Learning about these models helped me to become more knowledgeable in how computer systems transform code to light and vice versa. The model that first caught my interest was the OSI Model, which is the format that I will focus on here.
What Is the OSI Model?
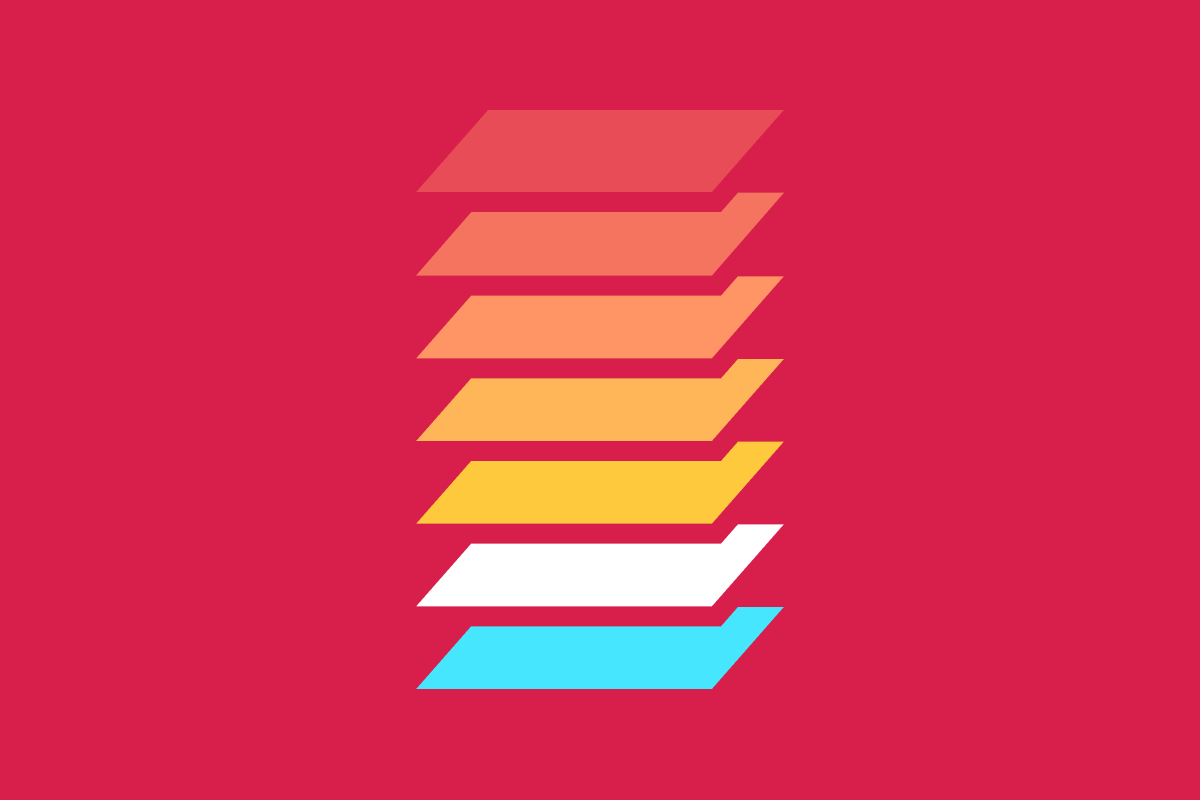
Let me preface this breakdown by saying that the OSI model is not the standard in how our networks communicate today, but it did serve as a framework to get to the more widely adopted TCP/IP model. The OSI model is simply an idea about how our computer network systems can communicate. It has become one of the pioneering concepts for how we communicate through multiple layers of network transmission by using necessary components, from physical computer parts to fully built applications. This network communication process involves seven layers:

By using layers, we can separate the responsibilities of the network communication process, which makes things easier to troubleshoot. Learning each layer’s responsibility helps us understand how our data is managed and transformed.
The Application Layer: What It Is and Why It’s Important
The application layer is where applications can initially make network requests to send down the pipeline. This is usually where users can send messages, request web pages, or download music by interacting with our devices. These interactions become messages that typically travel through the code that we write, destined to become signals that will shoot light beams to any distance.
This layer is important because it focuses on how our network requests choose initial communication protocols. These protocols will give specific information about how we want our network request to be sent. One of the most popular protocols is HTTP, which is used by Google Chrome, Safari, and Firefox to send and receive information displayed on web pages. Communication from this protocol is sent to or received from the presentation layer.
The Presentation Layer: What It Is and Why It’s Important
Because our network requests come from other applications, they need to communicate with your Operating System. Whether you use OSX, Windows, or Linux, this layer helps translate what the browser or other applications data consists of to make it more universally digestible for other computer processes.
This layer is important because it helps translate the application code into code geared to send over a network. When we want to send data, we can’t send it as a regular “string,” a.k.a. text. Even if you are sending a network transmission that consists of just a few letters, such as your name, it must be converted to 1s and 0s (binary) for it to be readable by the other parts of the network transmission process. The presentation layer is also important because it involves encrypting information before it is sent over a network or decrypting a network transmission if we are receiving data.
The Session Layer: What It Is and Why It’s Important
The session layer is responsible for creating, regulating, and destroying connections between systems. Once the operating system knows that it needs to send data, this layer manages how long that connection should remain open and ensures that we receive all of the information we are requesting or sending before terminating itself.
When we send data, it does not reach our devices all at once. Think of the session layer as a traffic light that signals us when we have more information. When that process is completed, it prevents unnecessary data from reaching our system. This layer also handles a bit of authentication so that we can trust that the data reaching us is coming from the place that we requested.
The Transport Layer: What It Is and Why It’s Important
The transport layer controls the limits set on the information that we transport around our application process. This layer determines the size or block of information to transport and how fast that data can be transmitted to or from us.
We can compare the transport layer to a highway. On this road, we are getting information about a truck that has our valuable cargo on it. The truck can go at a certain speed, and we’ve informed the packing company of exactly how many items we need on the back of that truck. In other words, the transport layer is essentially making sure that the cargo (data) is supplied in a way that we anticipate. Most network services usually utilize two transporting protocols: TCP (Transmission Control Protocol) or UDP (User Datagram Protocol). We may use TCP if we want reliable, stellar data that we can’t afford to lose (e.g., FTP & email), or UDP when we need fast data and may be okay with the occasional packet drop (e.g., live streaming, online gaming, etc.).
The Network Layer: What It Is and Why It’s Important
The network layer, also known as “level three,” is responsible for managing the movement of data from one host computer to the next. It allows packet management to find the shortest route to where the data needs to go. This is controlled by packet management devices such as a router.
Routers have long saved us by identifying which computer is sending a message. Being able to give computers logical addresses so that data can be requested or received is beneficial because we don’t want data floating around the internet– it should have a specific destination. Routers examine a frame, which essentially is data that contains a source and destination address. This frame also includes a “Payload”—a.k.a. the piece of data sent down the pipeline. This layer uses IP addresses to ensure that network requests go to the intended computer.
The Data Link Layer: What It Is and Why It’s Important
The data link layer, also known as DLL or “layer two”, is a complex layer that divides itself into two additional layers called the Logical Link Control (LLC), and the Media Access Control (MAC). This layer ensures that the delivery from computer node to computer node is complete. It is usually controlled by the Network Interface Card (NIC).
This part of the network request dictates how two machines talk to one another. The “frames” that the network layer examines are assembled by the data link layer. The MAC portion helps us to avoid collisions of our data if we send multiple requests while also establishing the medium in which our data will be sent (wireless vs. wired). The main job of the LLC is to identify our network protocols and analyze our frames for errors.
The Physical Layer: What It Is and Why It’s Important
The last layer of the network application process is handled on the physical layer. This is where modems, cables, or hubs handle data. It captures the whole frame data and converts the data transmissions to bits.
Light travels through fiber optic cables at 124,188 miles per second—that’s fast! We use satellites, fiber optic cables, routers, modems, and many other physical interfaces to send data from one world location to another. The physical layer is all about doing the heavy lifting by transporting our light waves at “warp” speed.
Conclusion
These layers allow us to conceptualize what a complete network transmission, from top to bottom, would look like. Our data will traverse each layer, and convert the code that we write into data that different protocols can interpret. If we want better insight into how modern networks have used this as a realistic platform, we can also look at the TCP/IP model to see what layers are used in today’s network transmissions.
Additional Reading: